MCA Microsoft Identity & Access Admin + MCA Microsoft Information Protection Admin
No related bootcamps found.
What's Included
2 Microsoft Test Vouchers
2 Microsoft Official Courses
1 Retake Voucher Per Exam
Microsoft Study Labs & Sims
Onsite Pearson Vue Test
Instructor Led Classroom Training
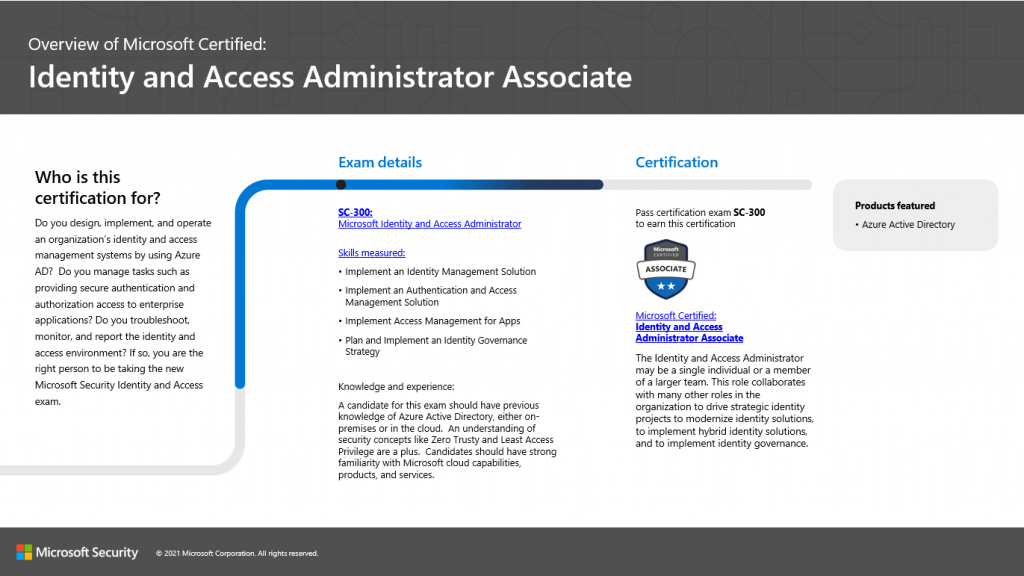
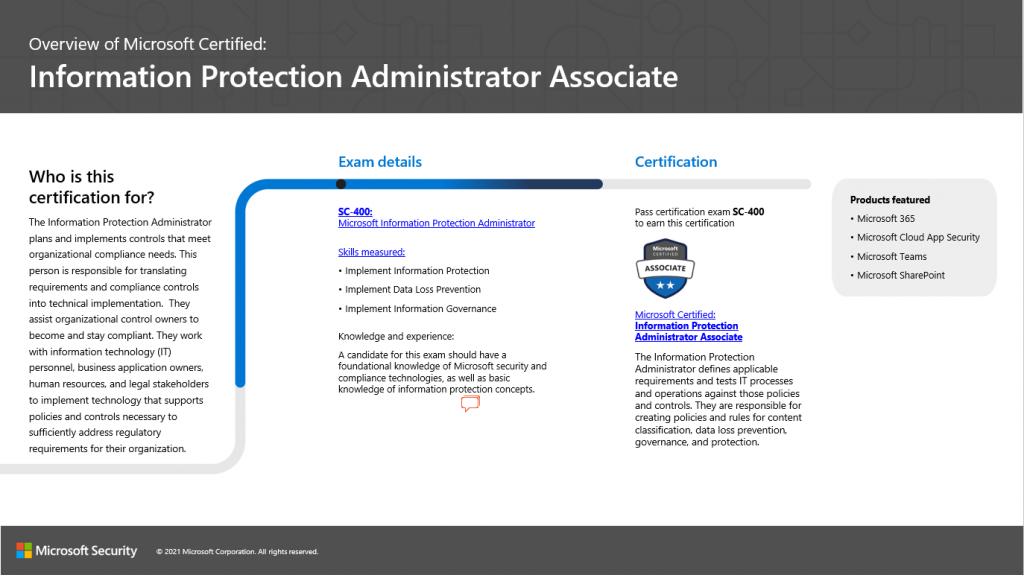
The MCA Microsoft Identity & Access Admin + MCA Microsoft Information Protection Admin - 6 day Boot Camp prepares students to design, implement, and operate an organization’s identity and access management systems by using Azure AD. The camp also teaches administrators how to creat policies and rules for content classification, data loss prevention, governance, and protection.
The MCA Microsoft Identity & Access Admin + MCA Microsoft Information Protection Admin Associate boot camp is taught using TWO Microsoft Official Courseware Courses
SC-300T00: Microsoft Identity and Access Administrator
SC-400T00: Microsoft Information Protection Administrator
While attending this 6 day camp - students will take two exams (SC-300 / SC-400) to achieve TWO Microsoft Certifications - Microsoft Certified: Identity and Access Administrator Associate - AND - Microsoft Certified: Information Protection Administrator Associate Certifications. This hands on, instructor led live camp focuses on the real world responsibilities of an Microsoft Security Administrator covering the information needed for the certification exams which are administered while attending.
Skills Gained:
Implement an identity management solution
Implement an authentication and access management solutions
Implement access management for apps
Plan and implement an identity governance strategy
Explain and use sensitivity labels.
Configure Data Loss Prevention policies.
Secure messages in Office 365.
Describe the information governance configuration process.
Define key terms associated with Microsoft’s information protection and governance solutions.
Explain the Content explorer and Activity explorer.
Describe how to use sensitive information types and trainable classifiers.
Review and analyze DLP reports.
Identify and mitigate DLP policy violations.
Describe the integration of DLP with Microsoft Cloud App Security (MCAS).
Deploy Endpoint DLP
Describe records management
Configure event driven retention
Import a file plan
Configure retention policies and labels
Create custom keyword dictionaries
Implement document fingerprinting